The Rise of Vehicle Connectivity
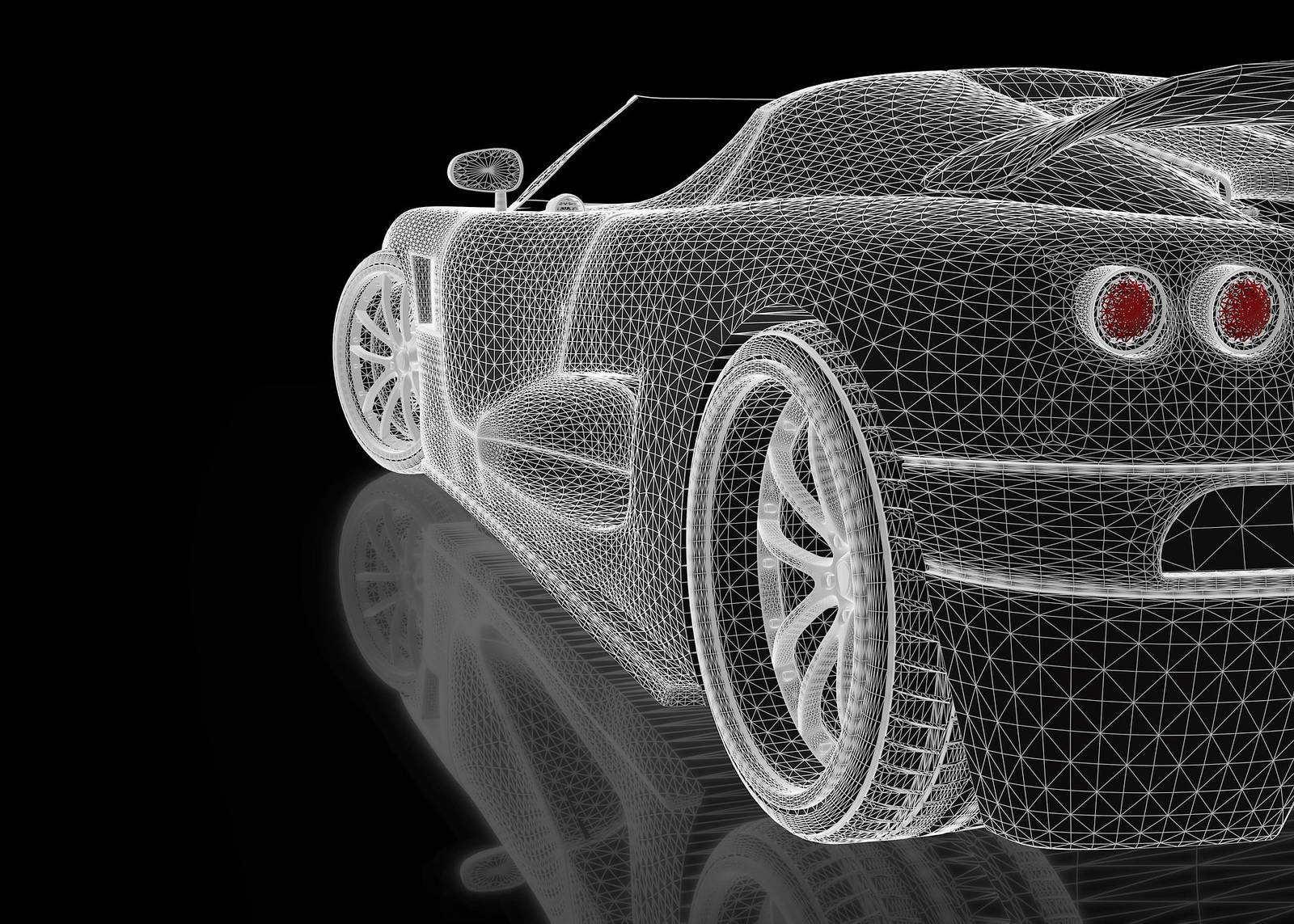
Art of Car Hacking Modern vehicles are more than just modes of transportation; they are now sophisticated computers on wheels. With the advent of connected cars, the automotive industry has embraced technologies such as telematics, infotainment systems, and autonomous driving features. These advancements enhance the driving experience but also introduce potential vulnerabilities.
Methods of Car Hacking
Remote Exploitation Car hackers often exploit vulnerabilities in a vehicle’s software or hardware through remote access. This can include infiltrating the car’s systems through Wi-Fi, Bluetooth, or cellular connections. Once hackers gain access, they can manipulate various functions, from steering and braking to infotainment systems.
Keyless Entry Attacks ECU Manipulation
Keyless entry systems have made it convenient for drivers to unlock and start their cars, but they are susceptible to relay attacks. Hackers use devices to intercept signals between the key fob and the car, effectively allowing them to unlock and steal the vehicle. The Electronic Control Units (ECUs) in modern cars control critical functions like engine management and braking systems. Hackers can gain access to these units and modify their programming, potentially causing accidents or disabling safety features.
Malware and Phishing
Just like your computer or smartphone, a vehicle’s infotainment system can be targeted with malware or subjected to phishing attacks. Unsuspecting drivers may download malicious apps or click on links that compromise the car’s security. In some cases, hackers may physically access a vehicle’s internal systems by tampering with onboard diagnostics (OBD) ports or gaining access to the car’s internal network through USB ports.
The Consequences of Car Hacking
Car hacking can have severe consequences, including The ability to remotely manipulate a vehicle’s controls poses grave safety risks, potentially leading to accidents, injuries, or even fatalities. Connected cars collect a wealth of data about drivers and their habits. A breach of this data can lead to privacy violations and identity theft. Car hackers can steal vehicles by disabling security systems or exploiting keyless entry vulnerabilities. Repairing a hacked vehicle can be costly, not to mention the potential for insurance complications.
Ensuring Vehicle Cybersecurity
Manufacturers regularly release software updates to patch vulnerabilities. If your vehicle has a connected app or Wi-Fi, ensure it has a strong, unique password. If you don’t use certain connected features, disable them to reduce potential entry points for hackers. Consider adding an aftermarket firewall to your vehicle’s network to monitor and block suspicious activity. If available, enable 2FA for any connected services related to your vehicle. Be careful when installing third-party devices or apps in your vehicle, as they may introduce vulnerabilities. Ensure your vehicle is physically secure by parking it in a well-lit area and, if possible, a locked garage. Stay informed about cybersecurity best practices and the latest threats in the automotive industry.
Conclusion
The Art of Car Hacking is a concerning reality in our increasingly connected world. With the rise of connected vehicles, it’s crucial for both manufacturers and drivers to prioritize cybersecurity. By understanding the methods employed by hackers and implementing preventive measures, we can minimize the risks associated with car hacking and ensure the safety and security of our vehicles on the road. Ultimately, the art of car hacking is a battle between hackers and security experts, with the latter continually working to stay one step ahead in the ongoing quest for vehicle cybersecurity.